If you're reading this, you've probably already noticed that your computer isn't performing like it used to. In the worst case, a Trojan has made its unwanted presence on your system known to you.
As we'll show you below, there's no cause for concern: There are plenty of easy ways to remove malware from your system and reclaim your digital domain.
Since a Trojan is just the tool malware uses to infect your computer, you're most likely noticing the impact of these programs, rather than the Trojan itself. If you've become the latest victim of ransomware, check out our EXPERTE.com guide for removing ransomware. Below, we'll show you how to remove most types of Trojans and their accompanying malware from your system.
Download a Free Malware Scanner
Removing a Trojan from your system doesn't need to be expensive or take a long time. There is free software that checks your system for malware and removes it in a matter of minutes. To show how easy this can be, we've used Malwarebytes.
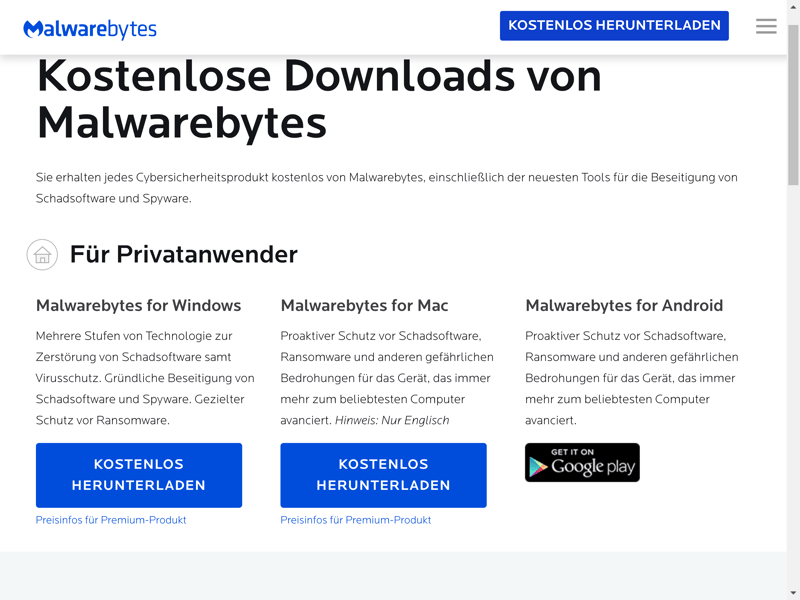
Malwarebytes is available for Windows, macOS, and Android.
After downloading and installing the software, you can activate a license, or purchase a subscription package. We're using the free version of Malwarebytes for this example. A Premium subscription unlocks all security tools, however, if you're already facing a Trojan, these won't be much help. You can take advantage of a free 14-day trial of the software's full version without having to input any payment methods.
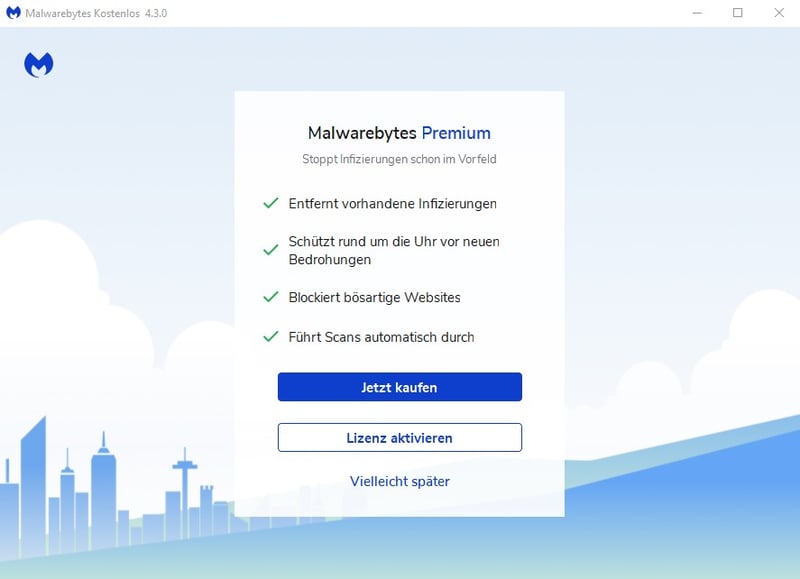
Apart from its very popular free version, you can purchase a Malwarebytes Premium license to unlock even more features and tools.
Guide: Remove a Trojan with Malwarebytes
1. Click on Scan to analyze your system. Depending on how large it is, this might take a few minutes. While scanning, Malwarebytes checks your files and programs for malware.
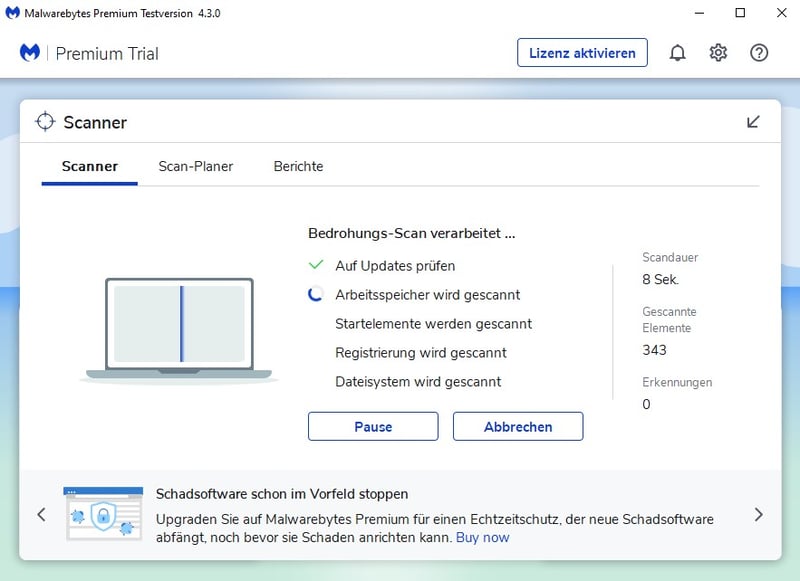
Malwarebytes scans your computer for infections, but you can continue going about your business.
2. Once the scan has finished, you can review its results. Malwarebytes lists all of the threats that it found, and you can quarantine them if desired. Once quarantined, these files can no longer damage your system.
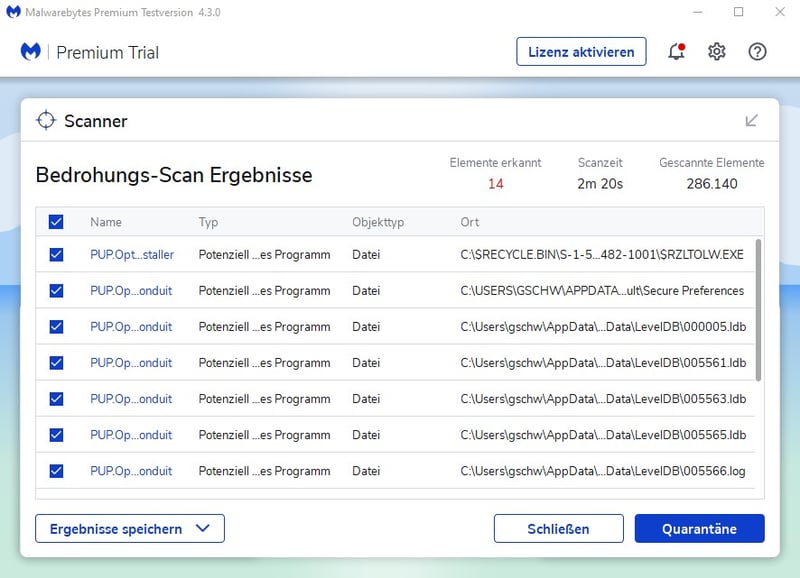
Once quarantined, malware files can't damage your system.
3. You can remove quarantined files from your system by clicking on Detection History. Simply select what you want to delete and click the Remove button at the bottom of the window. Should Malwarebytes have moved important files to quarantine by accident, you can also release them by following the same process and clicking on Restore instead.
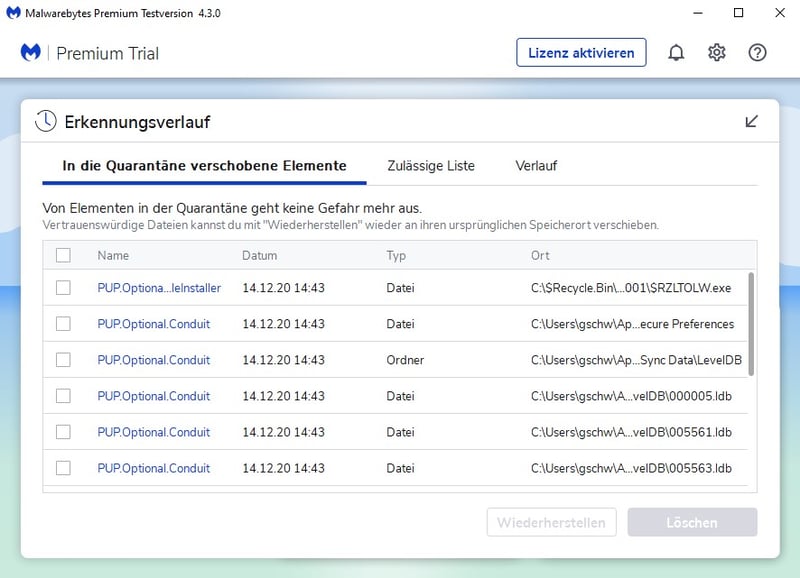
You can review dangerous or harmful files in Malwarebytes Quarantine.
Malwarebytes isn't the only free program that can help with Trojans. Most antivirus programs offer freemium versions of their software. These provide access to basic features while keeping advanced tools behind paywalls in the hope that users will upgrade to a premium subscription. If you plan on using one of them, you should expect some in-app marketing or advertising, however, this is a small price to pay.
For more information, be sure to check out EXPERTE.com's list of the best free antivirus software. Leading our evaluation was Avast Antivirus, thanks to its real-time protection and password manager, even for non-subscribers.
Rescue Disk/USB Device
If the malware scan didn't heal your system's infection, and/or the Trojan hasn't been removed, you'll need a rescue disk. This is a bootable CD/DVD or USB device that helps identify malware on your system. One example is Kaspersky Rescue Disk, which we'll show you how to use below.
Guide: Eliminate Trojans with Kaspersky Rescue Disk
1. Start by downloading the Kaspersky Rescue Disk image from Kaspersky's website.
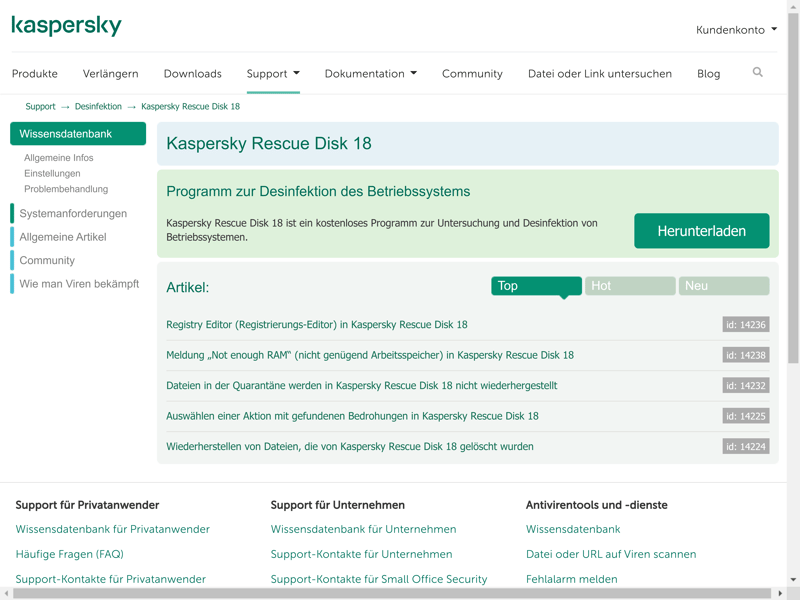
The Kaspersky Rescue Disk image can be downloaded for free.
2. Burn the image to a CD/DVD, or copy it to a USB storage device.
For the first option, Kaspersky recommends Windows users burn the image with ISO Recorder or DeepBurner.
To copy the image to a USB storage device, you can use Rufus on Windows or the integrated dd tool on Linux and macOS.
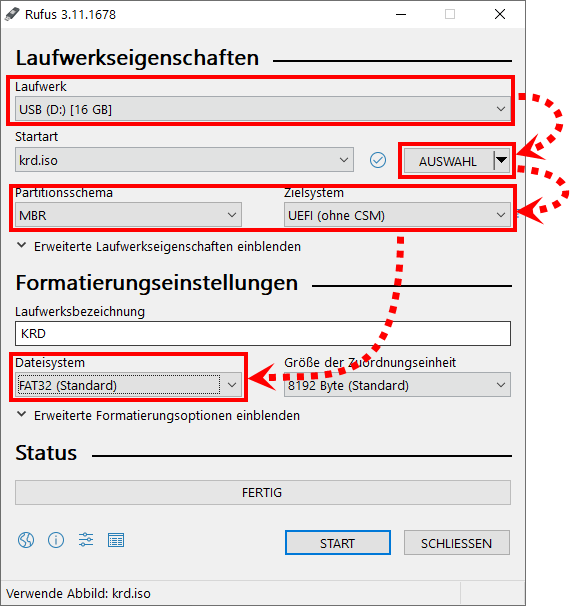
The USB device needs at least 1 GB of storage space (Image Credit: Kaspersky).
3. Put the burned CD/DVD in your disc tray, or connect the USB device to your computer. After this, you'll need to tell your system to boot from the CD/DVD or the USB storage device the next time it starts. Enter the BIOS menu to do this.
4. There are a few different ways to enter the BIOS menu in Windows, depending on which version of the software you are using. For Windows 10 users, click on the arrow next to Shut Down in the Start menu and, while holding down the Shift key, select Restart. In the menu that opens, click on Troubleshoot > Advanced Options and select UEFI Firmware Settings. Then click on Restart, and you'll enter the BIOS menu.
For other Windows versions, simply restart your computer and continually press the BIOS hotkey, which is usually F2 or F10 (depending on the manufacturer of your PC or laptop). If unsure of what the hotkey is for your system, you can usually see it somewhere on your (black) startup screen or check online.
5. Once in the BIOS menu, adjust the boot order. Move your CD/DVD drive or the USB device to the first position and press the F10 key to save changes.
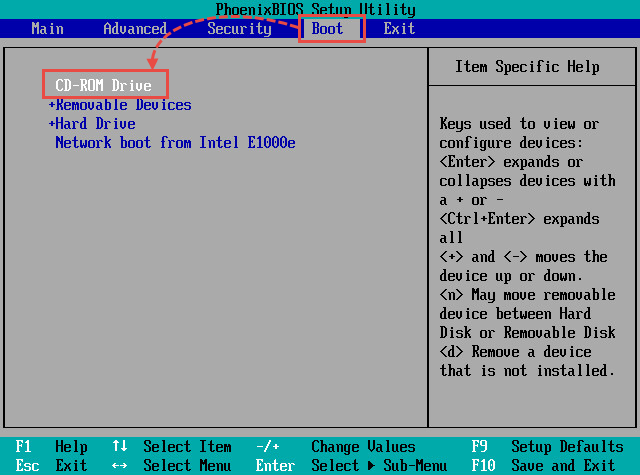
Tell your system to boot from the rescue CD/DVD or USB device (Image Credit: Kaspersky).
6. After the next restart, you'll wind up in Kaspersky Rescue Disk's user interface. Follow the software's instructions and, if possible, select Graphic Mode, to start the graphic user interface.
7. Select Kaspersky Rescue Tool from the start menu (in the upper part of the screen).
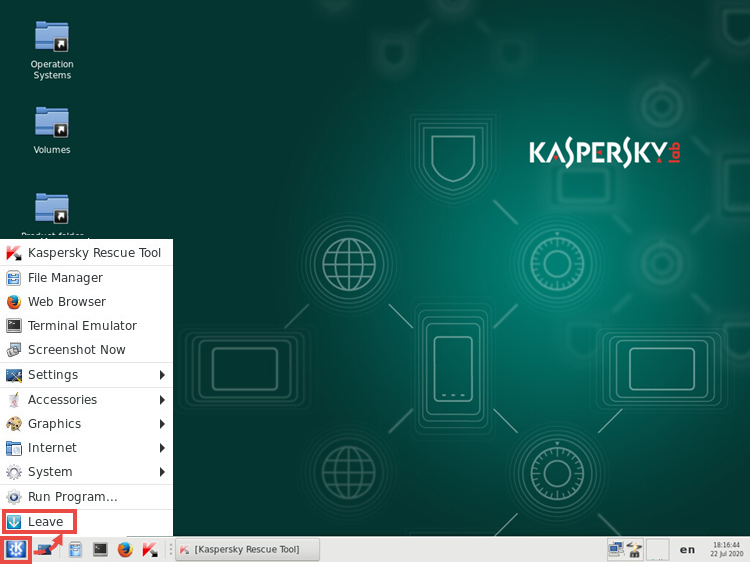
Use Kaspersky Rescue Disk to check your system for malware and remove any infections that are found (Image Credit: Kaspersky).
8. Click on Start scan to begin an analysis of your system. If you'd like to change where and what the tool scans, click on Change parameters.
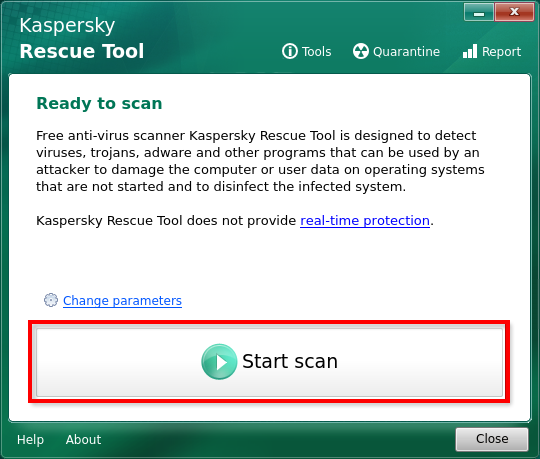
Kaspersky Rescue Tool finds Trojans, viruses, and more (Image Credit: Kaspersky).
9. If any threats are found, you can either quarantine or delete them. This can be done for all threats simultaneously, or for individual elements.
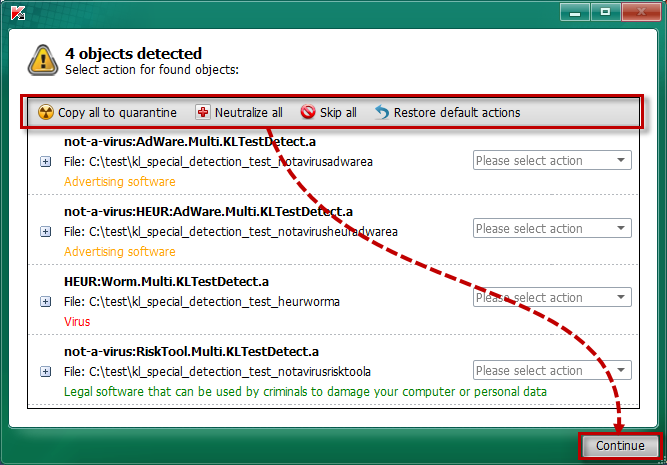
You can see which type of threats were uncovered and choose how you'd like to proceed on the results page (Image Credit: Kaspersky).
10. If an active infection has been identified, the tool will notify you. After that, you can disinfect your system either with or without a full scan, whereby Kaspersky recommends the first option, even though this takes longer.
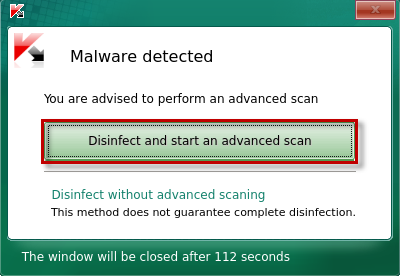
We always recommend performing an advanced scan if malware is discovered on your system (Image Credit: Kaspersky).
11. Once your system has been disinfected and all threats are neutralized, you can restart normally. To do this, click on Leave and then Restart in the Rescue Disk user interface's start menu.
12. When restarting, press the F2 or Delete key to return to the BIOS menu. In the Boot tab, move Hard Drive to the top, and save your changes by pressing F10. After restarting, everything should be back to normal.
Real-Time Protection With Bitdefender, Our Winner

Kaspersky Rescue Tool is great at removing malware from your system, however, it doesn't protect you against new threats. To keep your system Trojan and malware-free, you're going to need real-time protection, like that offered by most anti-malware providers.
The top service from EXPERTE.com's review series was Bitdefender, which secured first place in our rankings thanks to its high testing lab scores, user-friendliness, and selection of features.
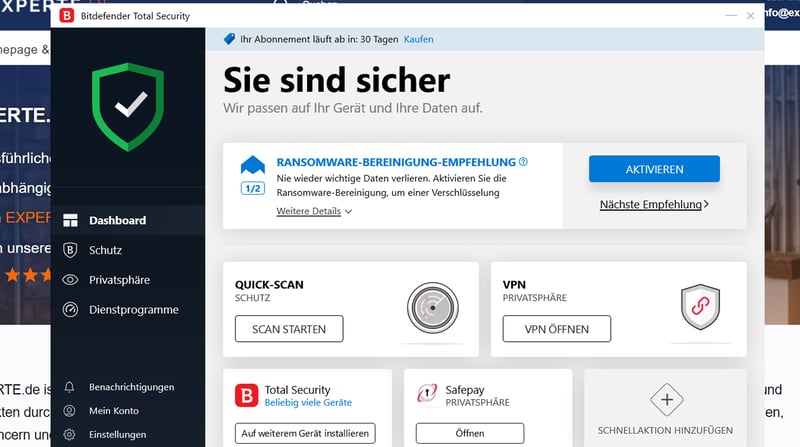
Bitdefender's clear user interface was just one of the software's many that greatly impressed us.
With Bitdefender, you can adjust real-time protection to your exact needs, setting when and how often it should check files. The program also protects against email, web, or webcam attacks, as well as ransomware, and of course, provides a firewall.
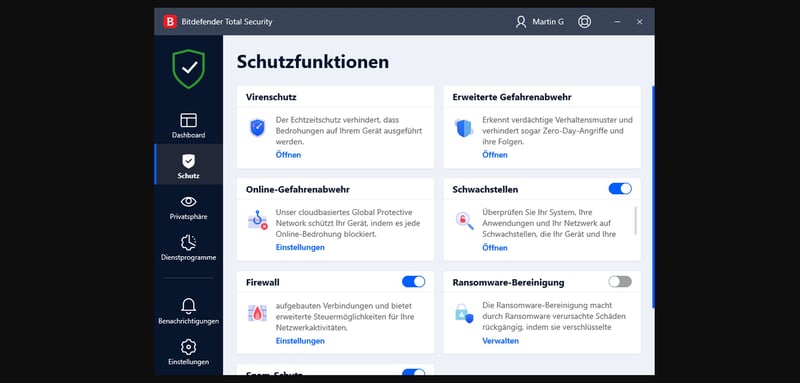
Bitdefender's package of features is truly remarkable.
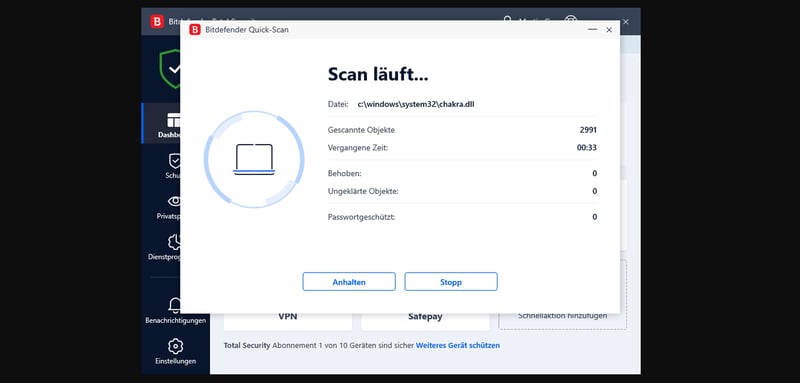
If you have a bad feeling that something is wrong with your system, you can also easily customize and perform a full scan with Bitdefender to put your mind at ease.
And if you need more convincing: Bitdefender subscribers also get a password manager, VPN, 24/7 support, a live chat, and solid mobile apps for iOS and Android devices.
Bitdefender doesn't just protect against Trojans but also gives you all the tools you need to handle nearly any kind of digital threat.

Conclusion
Trojans are dangerous, and removing them is tricky and time-consuming. However, like every sort of digital danger, you can reduce your risk of being infected by following a few basic guidelines: Don't download files or programs from shady or untrustworthy sites, and double-check emails before downloading or opening their attachments.
If it's too late for prevention, there are free and premium tools that help remove Trojans and other nasty programs from your system, and keep it protected down the road. For long-term security and prevention, you'll need reliable antivirus software. We've looked at some of the most well-known and popular antivirus solutions on the market and tested them in our EXPERTE.com reviews, to help you make your decision.