Internet Censorship Check



Internet Censorship Check: Site Blocked in China, Russia or Turkey?
Around the world, a number of governments block critical or undesirable websites. Prominent examples include China, Russia, and Turkey. With the EXPERTE.com Internet Censorship Check you can find out whether a website is blocked in any of these countries.
Examples
Here are some examples of websites that are blocked in one or more of the countries above.
How It Works
To ensure that the check is accurate, EXPERTE.com uses its servers in China, Russia, and Turkey. When you query us to check a specific website, we send the URL to each of these servers and try to establish a connection from within that country to the website.
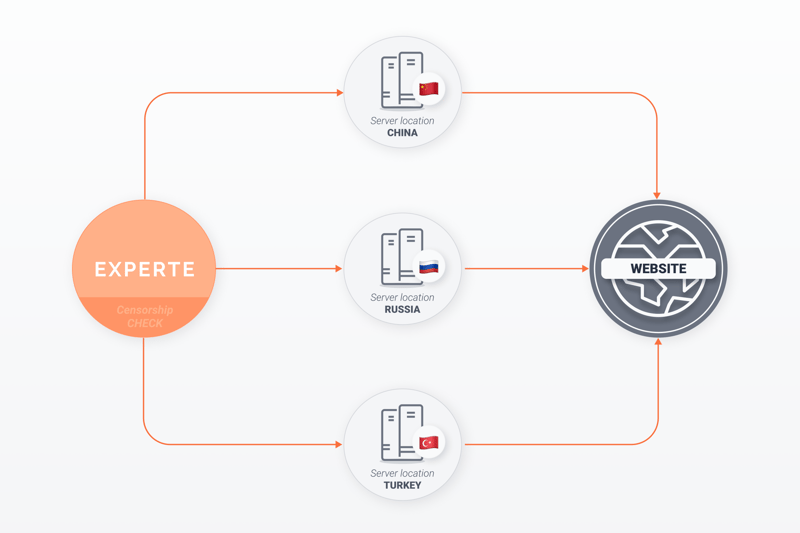
If the page is not accessible from the servers, its status will be noted as Blocked.
For control purposes we also check the website from servers in the US, Germany, and Hong Kong. If the site is not accessible from these locations, the requested website might be experiencing technical difficulties.










