Whenever someone mentions the Darknet, you might think of something dodgy and dangerous. However, most people who talk about it usually do so based on rumors and hearsay, not first-hand experience. Is the Darknet really so bad as its reputation?
We dived into the virtual shadow world and below, will let you know what we discovered.
Before we can explore the Darknet, it's important to briefly discuss the Internet's structure, specifically, the differences between the Clearnet, the Deep Web, and the Darknet. All three are part of the World Wide Web (WWW) but at different levels. Most who use the Internet only ever traverse the Clearnet.
Clearnet vs. Deep Web
Let's imagine the Internet like a large city. Any publicly accessible place in this city, such as a park, a shop, or a museum, is part of the Clearnet or surface web. You don't need special permission to enter any of these areas (for our example, this means that you can use a normal browser), and if you search for them on a map or in a telephone book (a search engine in the digital case), you'll find them.
However, just like any city, there are also places on the Internet that you need an invitation, ticket, identification, or key to access, such as private clubs, offices, concerts, or apartments.
In our example, all of these places are part of the Deep Web and include intranets, research databases, as well as internal pages operated by authorities. You won't find these sites through a search engine, but, you can access them via a normal browser, so long as you know their address and have login credentials.
Darknet: Virtual Hoods
Darknet (or Dark Web) pages cannot be found with either regular browsers or standard search engines. In our imaginary city, the Darknet can be visualized as an area that should be avoided at night, and even during the day isn't all that pleasant. Comparable to inner cities, the Darknet is full of action but dangerous. Online, people meet in these virtual 'hoods' for harmless, anonymous conversations as well as criminal plotting.
How Does the Darknet Work?
The Darknet is an isolated, peer-to-peer overlay network in which all participants manually create an encrypted connection between one another, rather than automatically, as is the case in regular networks. Darknet pages are also referred to as hidden services since they cannot be found with normal browsers.
When online in the Darknet, all data traffic is encrypted, even IP addresses, which are usually easy to follow. This ensures greater security and anonymity but also makes surfing somewhat slower.
How to Enter the Darknet?
But how to access the dark side of the World Wide Web if not through regular search engines and browsers? The answer is surprisingly easy, as you'll only need a special browser, Tor, a favorite for anonymous surfing in the Clearnet as well.
Tor is short for "The Onion Router", which relates to how the software operates. To ensure anonymity, Tor routes each data request through a randomly selected computer, known as a node, until it reaches an exit node, from which it enters the Internet.
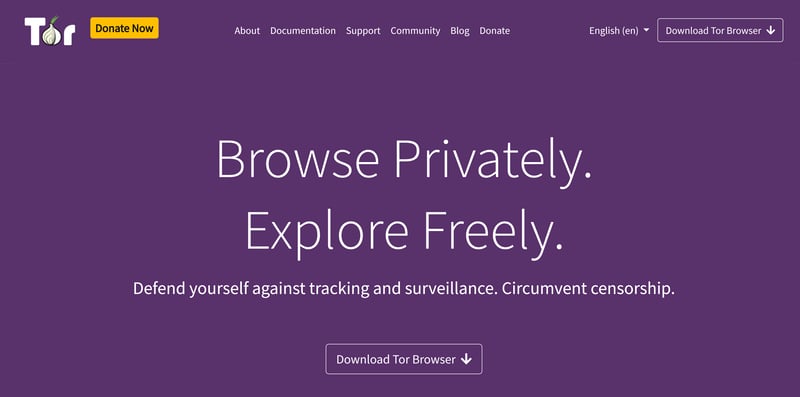
To enter the Darknet, you'll need to download and install Tor browser.
By default, Tor encrypts data several times, like the rings of an onion. Each computer that participates in a data transfer, encrypts one level. The main attraction? Should someone monitor your data flow, the packet that they see will appear completely different than what the node forwards. In this way, all traces are blended together, making it nearly impossible to reconstruct them.
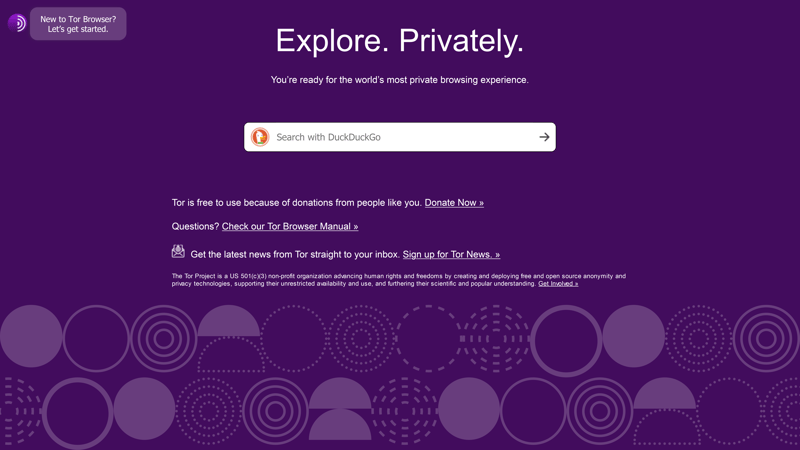
It's also possible to anonymously surf the Clearnet with Tor browser. DuckDuckGo is the default search engine.
Onion Links: Navigating the Virtual Shadow World
Once you've downloaded and installed Tor, your system should connect to the network without issue. Now, you'll need to choose: Normal, anonymous surfing in the Clearnet, or a trip to the Darknet. To do the latter, it's necessary to step a bit deeper.
As mentioned above, regular browsers and search engines don't work for Darknet pages, so you'll need to use Darknet search engines like Ahmia.fi or Torch. Don't expect domains to end in .com either, since all Darknet addresses instead consist of combinations of letters and numbers with the ending .onion.
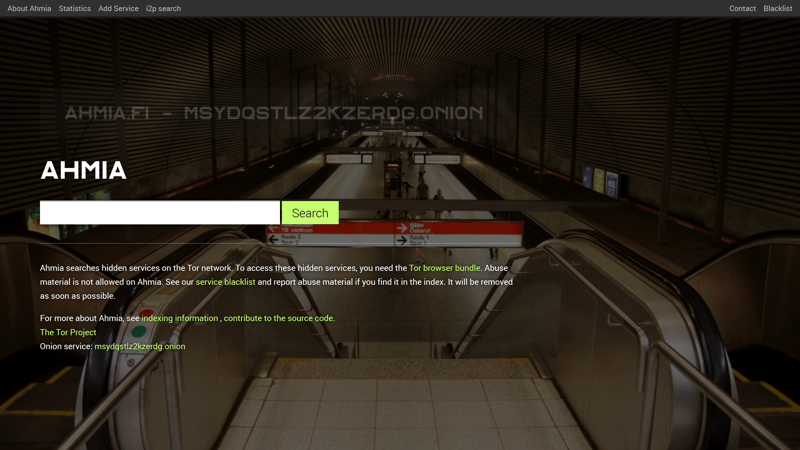
Ahmia is one of the Darknet's most popular search engines.
Those who operate Darknet sites are rarely made public. As such, it's almost impossible to censor or take down .onion pages.
Why Use the Darknet?
Using the Darknet makes sense for anyone who wants to remain anonymous and protect their privacy.
For most of us, when surfing the Clearnet, we leave traces of our activity and behavior. Suppose that you've just searched for a hotel in Las Vegas. Within a few days, ads for the city will appear in pop-ups and web banners. After hundreds or thousands of searches, companies like Google create a fairly accurate user profile for you to sell more ads and generate revenue. Over time, your anonymity and privacy all but vanish.
Tor prevents the above, but it's also life-saving for dissidents and journalists in countries where the flow of information is tightly managed by authorities or dictators. It might sound surprising, but plenty of news agencies, such as the New York Times maintain .onion pages. Whistleblowers also utilize the Darknet for its ability to encrypt data and anonymously communicate online.
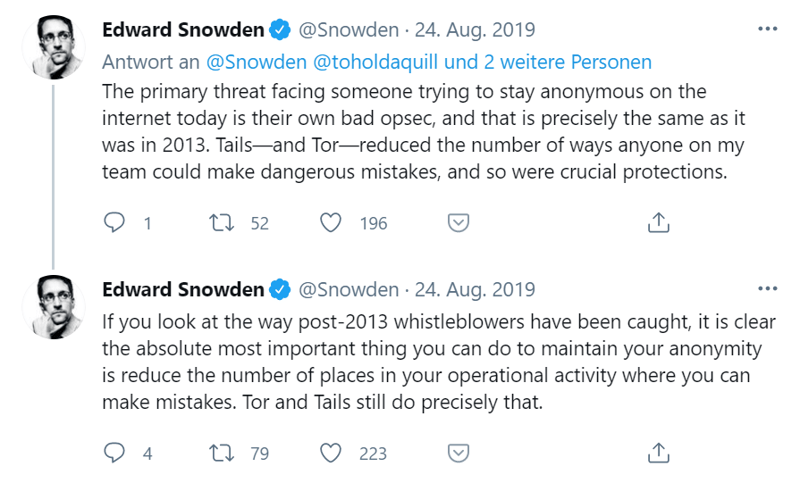
Edward Snowden, who released a cache of top-secret NSA documents, cites Tor as one of the most important tools for online anonymity.
Nerds and techies also flock to the Darknet, since they're able to find like-minded individuals with whom they can freely and openly communicate.
According to Tor's developer, Roger Dingledine, more than two million people use the anonymous browser every day to surf anonymously and circumvent state censorship. Only 1-3% of Tor users access the Darknet through the browser, which explains why the most visited websites (according to CHIP, a tech magazine), are Facebook, OnionShare (a file-sharing service), and news portals.
The Black Sheep
Anything can be misused or abused. During our research, we determined that a large amount of content on the deeper Darknet exists which we are neither interested in, nor wish to see.
Can I Buy Things in the Darknet?
Yes, but it's better not to. Even though there are numerous marketplaces on the Darknet where you can purchase both legal and illegal goods, we advise against doing so for the following reasons:
Bitcoins are tracked and must be washed, which takes a long time and is illegal.
Goods need to be sent to a real address, whether digital or physical. This cancels any anonymity.
No protection is offered against fraud.
Most things for sale on the Darknet are illegal.
Is It Illegal to Access the Darknet?
So long as you don't do anything illegal, accessing the Darknet is 100% legal. Many of the goods and services offered for sale on the Darknet are not legal. The same rules that hold in real life apply to the Darknet: If purchasing drugs or weapons, you'll become criminally liable. The same applies to downloading pirated movies or music.
The German Federal Office for Information Security summed up the situation nicely: "Movement on the Darknet is not illegal in and of itself, but it is a security risk." Fraudsters hawking fake goods lurk around every corner for unsuspecting newbies, who they can infect with a Trojan or virus. Accordingly, it's important to enter the Darknet with a great deal of caution and observe the following rules:
Trust no one
Make sure your virus scanner is up to date
Tape over your webcam's lens
Never post personal data or pictures
Never download anything
Never buy anything
What Kinds of Sites Are on the Darknet?
Despite how easy it is to enter the Darknet, it's relatively difficult to find interesting or worthwhile things to do.
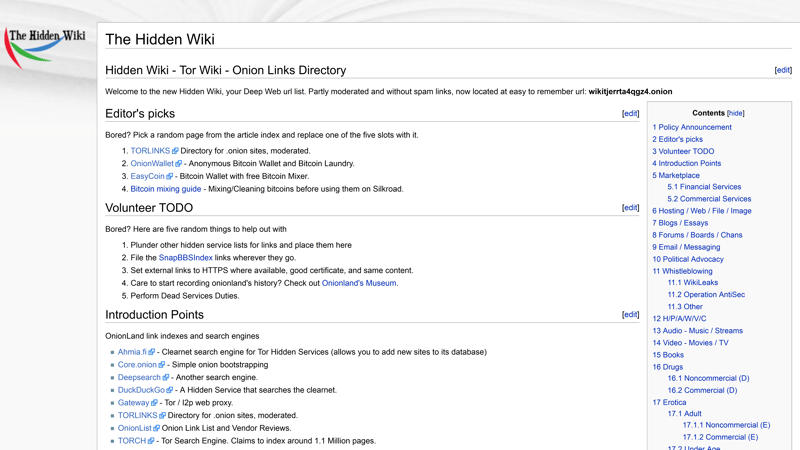
A good starting point for your first trip to the Darknet is a link index, like The Hidden Wiki.
To help, we found and tested a few interesting pages which are listed below. Your first stop should be an authoritative index like DeepLink Onion or a Tor-specific search engine like Ahmia or TOR66. It goes without saying, but you should also exercise caution when clicking on links contained in these search engines.
Name | Type of Site |
|---|---|
Search Engine | |
Search Engine | |
Search Engine | |
Search Engine | |
Link Index | |
Link Index | |
Link Index | |
News | |
News | |
Information About Surveillance Activities | |
Radio |
Conclusion
There are plenty of reasons to check out the Darknet. The most compelling is probably to take a first-hand look at something that most people avoid. Beyond that, it's also refreshing to read news and stories which aren't hyped or pushed by marketing algorithms. While visiting isn't illegal, it also isn't for the faint of heart. If you're only expecting to find journalists and dissidents, you're in for a rude awakening.
Anyone who is shocked by what is written on the Clearnet will probably have a heart attack from Darknet content. Some might find it thrilling to watch in real-time what is usually only shown on the silver screen or in TV shows. Others could come away from a trip to the Darknet with a better understanding of why humanity behaves the way it does.
Like basically everything digital, when snooping around the Darknet, try not to lose your sense of proportion or to throw caution to the wind.
With that said, the Tor browser is much more than just the Darknet, also providing a means for those who live under dictatorships to stay informed about what government propaganda doesn't report. It also greatly anonymizes surfing the Clearnet, making all Internet activity you engage in safer in the process. For that reason alone, installing and downloading the software is highly recommended.
FAQs
The Darknet is an anonymous, hidden part of the Internet, inaccessible with normal search engines or web browsers. You'll need special software to visit websites on the Darknet, the most well-known of which is Tor. Darknet sites don't have regular addresses but consist instead of combinations of numbers and letters. When using Tor, these end with the .onion domain name.
To enter the Darknet, you'll need special software, like the Tor browser. This browser can also be used to surf the Clearnet with greater anonymity. Tor looks very similar to other browsers like Firefox or Chrome, however, it offers greater functionality. Once you've connected to Tor, you can explore the Darknet or surf the Clearnet. Darknet pages have domain names that end in .onion.
No, neither downloading a Darknet-capable browser, like Tor nor surfing the Darknet are illegal. Most of the products and services that are offered on the Darknet are illegal though. If you visit a site with prohibited or illegal content, even by accident, you could be liable to criminal prosecution. A fine line exists between what is allowed and what isn't, so tread carefully.
The Darknet is great for securely sending emails or anonymously listening to a radio station. Through a reputable link index, you can even find funny or interesting pages. Tor browser can be used for surfing the Clearnet as well, making whatever you do there more anonymous. For precisely this reason, it's the go-to tool for journalists, dissidents, and whistleblowers.