You should never take the safety of your Internet connection for granted, especially when using a public network. So, why not bring your home network everywhere with you? No, not by carrying your router under your arm, but with a VPN. Using Raspberry Pi as a VPN server is a particularly convenient way to do this, and below we'll show you how.
A Raspberry Pi is an inexpensive mini-computer without a case, mouse, of any other of the traditional hardware. They were originally created to help children interactively learn about computers, but have become popular for routine functions owing to their low cost and easy replacement. By configuring your Raspberry Pi as a VPN, you'll be able to connect to it from anywhere.
Advantages of Using a Raspberry Pi as an OpenVPN Server
Raspberry Pi's biggest advantage is its low cost. Compared to a full Linux computer as a VPN server, you'll pay significantly less for hardware and upkeep. The device is also capable of staying connected to a network 24/7, doesn't require cooling, and uses a minimal amount of electricity, maintaining the integrity of your VPN tunnel.
Another major advantage is that OpenVPN's server software is completely free and available for most operating systems, including Windows, macOS, Android, iOS, and Linux.
Building a mini-computer is relatively simple and will help ensure that your VPN server is both stable and reliable.
Setup Preparations
You will need:
- 1.
A Raspberry Pi (ideally Model 2 or newer).
- 2.
A micro-SD flash memory card with Raspbian-Jessie installed.
- 3.
An Internet connection (either by network cable or WiFi) to Raspberry Pi.
- 4.
A micro-USB power connection.
Additionally, you should also consider if you want to connect your Raspberry Pi to a monitor, mouse, and keyboard, or if you would prefer to access the device using SSH. Usually, monitoring the server with SSH is the easiest option, since it allows you to access the Raspberry Pi through programs, like PuttY, WinSCP, or OpenSSH, installed on your main computer.
To access your Raspberry Pi with SSH, you only need to know the device's IPv4 address. Check your router when the Raspberry Pi is connected to your local network to find this out.
Adjust your IP Addresses
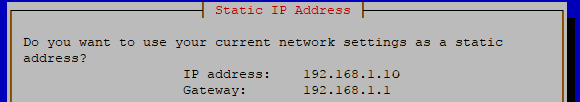
Should you want to connect to the VPN server using SSH, it's a good idea to assign it a fixed IP address as makes accessing it much simpler. For OpenVPN, it is also important that the server can be accessed by a fixed local IP address in your network.
The VPN server should have the same address when you access it remotely. Most Internet service providers (ISPs) assign their routers new, dynamic IP addresses every 24 hours, so you will also need to use a dynamic DNS (DDNS) service.
To do this, follow the steps below:
- 1.
Assign the VPN server a fixed IP in your local area network (LAN)
In your router's administrator area, you can assign the Raspberry Pi a fixed IPv4 address based on its Mac address. - 2.
Enable port forwarding on the router
With port forwarding, you'll make the fixed local IP address of your router accessible from outside of your LAN. OpenVPN uses port 1194. If your Raspberry Pi has an IP address of 192.168.1.10, then all of your router's UDP data traffic needs to be routed through port 1194. - 3.
Assign a hostname using a DNS service
To access your network from somewhere else, you'll need to set up a DDNS since your ISP likely alters your router's IP address every 24 hours. Alternatively, you could ask them if it is possible to be assigned a fixed IP address.
If this isn't possible, you can use a service like No-IP, which is supported by most routers. This gives your router a fixed hostname that is forwarded automatically to your new IP address when your router's IP address is changed. Installation instructions for No-IP can be found on the service's website.
Update Raspberry Pi
Before installing OpenVPN or Pi VPN, you should install all available updates for the device's operating system. This can be done by executing the following commands:
Change your username and password
To be on the safe side, we recommend changing your Raspberry Pi's default username and password ("Raspberry" and "Pi"). This can be done either locally, or over SSH using the following command:
2 Options: PiVPN vs. OpenVPN
OpenVPN is the most popular VPN solution for Linux systems, and by extension, for Raspberry Pi. The program is not only very secure, but also open source, and completely free. Since its installation through text-based commands is difficult, particularly for new users, PiVPN offers a much easier alternative.
Option 1: Set up a VPN Server With PiVPN
PiVPN is based on OpenVPN, which means that it is compatible with Linux and all of its current distributions including Raspbian, Debian, and Ubuntu.
Step 1: Install PiVPN
Since PiVPN uses a bash script, you don't need to download and install it like typical software. Rather, simply execute the following commands in the command prompt:
Step 2: Configure PiVPN
When PiVPN starts, you'll receive a notification that you should use a static IP address. If you have already assigned your router a fixed IP address (as recommended above) you can skip this step.
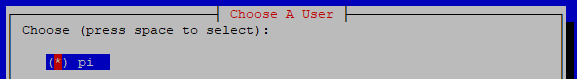
Finally, create a local user account, in which OpenVPN's configuration settings are saved. Here, select the user account you created, and in the next step, activate automatic updates (‘unattended upgrades‘).
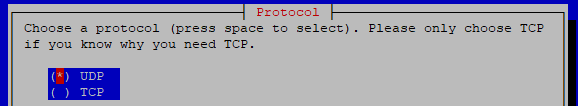
In the next dialog box, select UDP from the list of VPN protocols, leaving the recommended port number as 1194, so long as you've set this port for forwarding on your router (as recommended above).
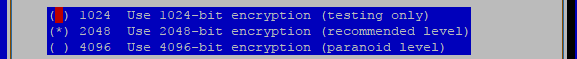
Key length can be kept at 2048-bit since this provides a high level of security. The time needed to create keys can vary depending on the Raspberry Pi model you're using.
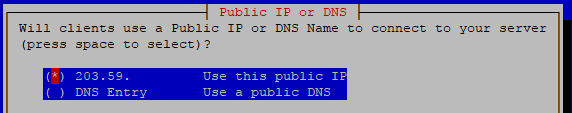
In the next step, you'll be asked if the VPN server is accessible by a fixed IP address, or hostname (‘DNS Entry‘). If a DNS service like No-IP is installed on your router, enter the relevant hostname here.
After restarting your computer, the initial setup is already complete.
Step 3: Add and Remove Network Clients
With PiVPN, installing and configuring the client is very straightforward. You only need to enter the following in the command prompt:
You'll then be asked for the desired username and password. After that, the configuration file will be named ‘[Client].ovpn‘ and saved in the ‘~/ovpns‘ folder.
You will only need this file for the client through which you access the VPN server since it contains all keys and server certificates. You can simply import them to any desired OpenVPN client.
Clients can be easily removed with the following command:
Option 2: Configure a VPN Server Using OpenVPN

For those more familiar with Linux, or desiring more choice in configuring their VPN server, OpenVPN offers an alternative to PiVPN.
Our step-by-step guide assumes that the most up-to-date version of Raspbian is being used. If you follow all of the steps below, configuring an OpenVPN server on your Pi is not particularly difficult, even without significant background knowledge.
Step 1: Install OpenVPN and Create an RSA file
The software, as well as the OpenSSL encryption protocol, are installed by executing the following command:
Once OpenVPN has been installed, copy the easy-RSA script to the corresponding configuration directory with the following command:
Next, open and modify the "vars" file (in the appropriate folder).
The line export EASY_RSA=“‘pwd‘“ needs to be replaced with the following:
You can also change the key length here. To prevent performance issues, on Raspberry Pi model 3's, you should use a 2048-bit key length. Since this will create problems for model 2's, you're best off using a 1024-bit key length, which will sacrifice a bit of security for improved performance. To adjust the encryption level, you only need to change the value in the line "export KEY_SIZE=" from 2048 to 1024.
Now, you can return to the easy-RSA configuration directory and start settings with root rights, by executing the vars script. Once complete, the configuration file will be made accessible through a symbolic link. This is accomplished by executing the following four lines:
Step 2: Create Certificates
The key files for OpenVPN will now be changed and then newly created. For the country name, enter "US". All additional prompts can be accepted.
Now, generate the key files with the following command:
Step 3: Set up a VPN Client
For each device that you intend to access your VPN server from, you'll need to set up a client. Each of these requires a certificate and the correct key. Here too, you'll need to enter the country code and assign the client a name. In our example, we named the client ‘desktop-pc‘.
Alternatively, you can use the command build-key-pass instead of build-key to generate a password for your client.
Creation of the certificates and the key is completed with the following command:
Finally, log the root user out using the exit command.
Step 4: Generate Configuration Data
OpenVPN's configuration data is generated with the following command:
This configuration data must be supplemented with a few additional pieces of information, which we'll describe in detail below. Make sure that UDP is selected as protocol, that routing via IP tunnel is activated, and that the port is set to its default (1194).
The SSL/TSL root certificate (ca), digital certificate (cert), and key need to be created in the easy-RSA directory. Make sure that you enter the correct encryption (1024 or 2048).
The command server 192.168.2.100 255.255.255.0 ensures that Raspberry Pi is used as the VPN server. With redirect-gateway def1 bypass-dhcp, all IP traffic is routed through the IP tunnel.
Next, you need to name the public DNS server that the VPN server will utilize. For example, 8.8.8.8 is a public DNS server used by Google. Of course, you can also use the IPv4 address of another DNS server. In this case, log information will be written to the openvpn file.
Finally, it's necessary to configure some additional parameters:
persist-key, ensures that key data is not read again, while persist-tun prevents the drivers from restarting.
With user nobody and group nogroup the daemon's rights are removed.
verb regulates the log file's completeness. By adding 0 no data is saved apart from error messages. We recommend a value of 3.
The client-to-client parameter allows us to define which other VPN clients are identified.
LZO compression is activated with comp-lzo.
Config data should now read as:
You can save your parameters by pressing Crtl+O. To exist the editor, hold down Crtl+X.
Step 5: Create a Script for Internet Access
In order to use the VPN tunnel to connect to your home network, you need to create a path. To do this, begin by creating an rplvpn file with the following command:
In this file, you'll be able to enter comments that serve as headers for the Linux-Init script. Beyond that, you can activate ip_forward, set iptables as packet filters for forwarding, and protect LAN and Internet access. The file should look like this when finished:
With Crtl+O and Crtl+X you can save and close the file, respectively.
To finish, you'll need to grant the script certain rights, which is done by entering the following command:
You can now execute the script, and restart the server.
Step 6: Complete Client Setup
You're almost there! Before finishing, you need to combine the certificates and keys from your client(s) and prepare them for export. To do this, again grant yourself root rights, and open the client file which you want to modify. For our example, we again used "desktop-pc".
Now, add information about your DNS provider in line 4 of this file, your static IP address (for example, 10.10.10.10) in line 10, and the name of your client in line 11. Save and close the editor with Crtl+O and Crtl+X. Once finished, the file should look like this:
Zip the configuration file together with the certificates and keys (should you not have a Zip packet installed, you can easily get one by entering apt-get install zip).
Then adjust the file's rights with chown pi:pi /home/pi/raspberry_desktop-pc.zip and finish setup with exit. The Zip file you've created can be transferred to your PC using SCP or SFTP software.
Thus, you've done everything and can immediately connect to your local network using Raspberry Pi and an OpenVPN server.











